by Cody Dumont
January 29, 2015
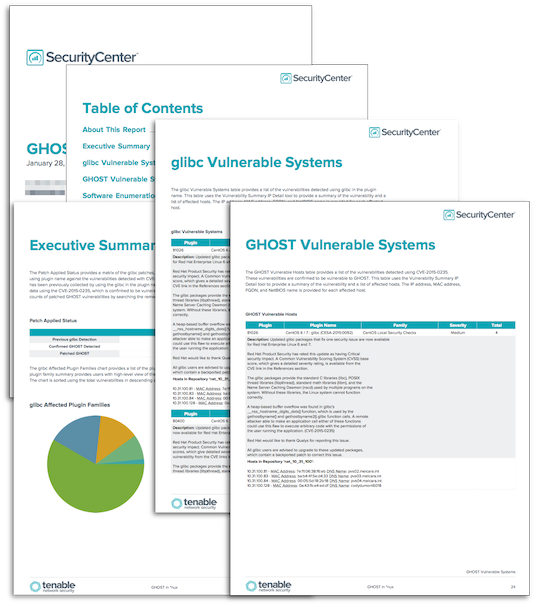
The newest high profile vulnerability is the GNU C Library (“glibc”) vulnerability, dubbed “GHOST” by the media. Organizations should take a proactive approach to patching these high profile vulnerabilities. This report helps identify vulnerable systems using several methods of identification.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Security Industry Trends. The report requirements are:
- SecurityCenter 4.8.2
- Nessus 6.1.1
The report uses three methods of identifying vulnerable systems. The first, and most accurate, method uses the CVE-2015-0235 filter to identify the systems scanned with newly released plugins. The second method searches the Software Enumeration (SSH), plugin 22869, for the affected libraries. The final method searches the plugin names for the string “glibc”. Using all three methods, the analysts will be able to identify vulnerable system even if they cannot be scanned immediately.
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. SecurityCenter Continuous View (SecurityCenter CV) provides a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. SecurityCenter CV’s proactive continuous monitoring identifies your biggest risk across the entire enterprise. SecurityCenter CV enables the organization’s security teams to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance.
Chapters
Executive Summary
- The Patch Applied Status provides a matrix of the glibc patches, and compares the vulnerabilities detected using plugin name against the vulnerabilities detected with CVE-2015-0235. The first row looks over data that has been previously collected by using the glibc in the plugin name. The second row searches vulnerability data using the CVE-2015-0235, which is confirmed to be vulnerable to GHOST. The last row provides the counts of patched GHOST vulnerabilities by searching the remediation database for CVE-2015-0235.
- The glibc Affected Plugin Families chart provides a list of the plugin families with glibc vulnerabilities. The plugin family summary provides users with high-level view of the affected operating systems and applications. The chart is sorted using the total vulnerabilities in descending order.
- The Top 10 glibc Affected Subnets chart provides a list of the top 10 subnets with vulnerabilities related to glibc. Presenting data in this manner allows analysts to see the subnets at the most risk so that remediation efforts can be prioritized. The bars represent the total hosts with a glibc vulnerability, and bars are sorted in descending order.
glibc Vulnerable Systems
- The glibc Vulnerable Systems table provides a list of the vulnerabilities detected using glibc in the plugin name. This table uses the Vulnerability Summary IP Detail tool to provide a summary of the vulnerability and a list of affected hosts. The IP address, MAC address, FQDN, and NetBIOS name is provided for each affected host.
GHOST Vulnerable Hosts
- The GHOST Vulnerable Hosts table provides a list of the vulnerabilities detected using CVE-2015-0235. These vulnerabilities are confirmed to be vulnerable to GHOST. This table uses the Vulnerability Summary IP Detail tool to provide a summary of the vulnerability and a list of affected hosts. The IP address, MAC address, FQDN, and NetBIOS name is provided for each affected host.
Software Enumeration
- The Software Enumeration (glibc) table provides a list of hosts known to have glibc installed using the software enumeration plugin. Due to several methodologies used in software enumeration and vulnerability detection, this table uses a different method to identify systems that may be vulnerable to GHOST. The Software Enumeration (SSH) plugin (22869) analyzes the system and attempts to identify all of the software packages that are installed. This method of vulnerability detection can be effective as a validation of vulnerable software present, or to validate if the applicable patches have been applied. The table uses the Vulnerability Detail tool, and provides the full list of packages detected during software enumeration.