Tenable Security Center
すべての資産をリアルタイムで可視化してセキュリティの重点項目を予測するオンプレミス管理製品
IT、セキュリティ、コンプライアンスをリスクベースで捉えて、最も重要な資産や脆弱性をすばやく識別して優先順位を付けます。
オンプレミスで管理される、Tenable Nessus を搭載した Tenable Security Center 製品スイートは、お客様のネットワークをリアルタイムで継続的に評価し、業界で最も包括的な脆弱性カバレッジを提供します。完全なエンドツーエンドの脆弱性管理ソリューションです。
デモを予約する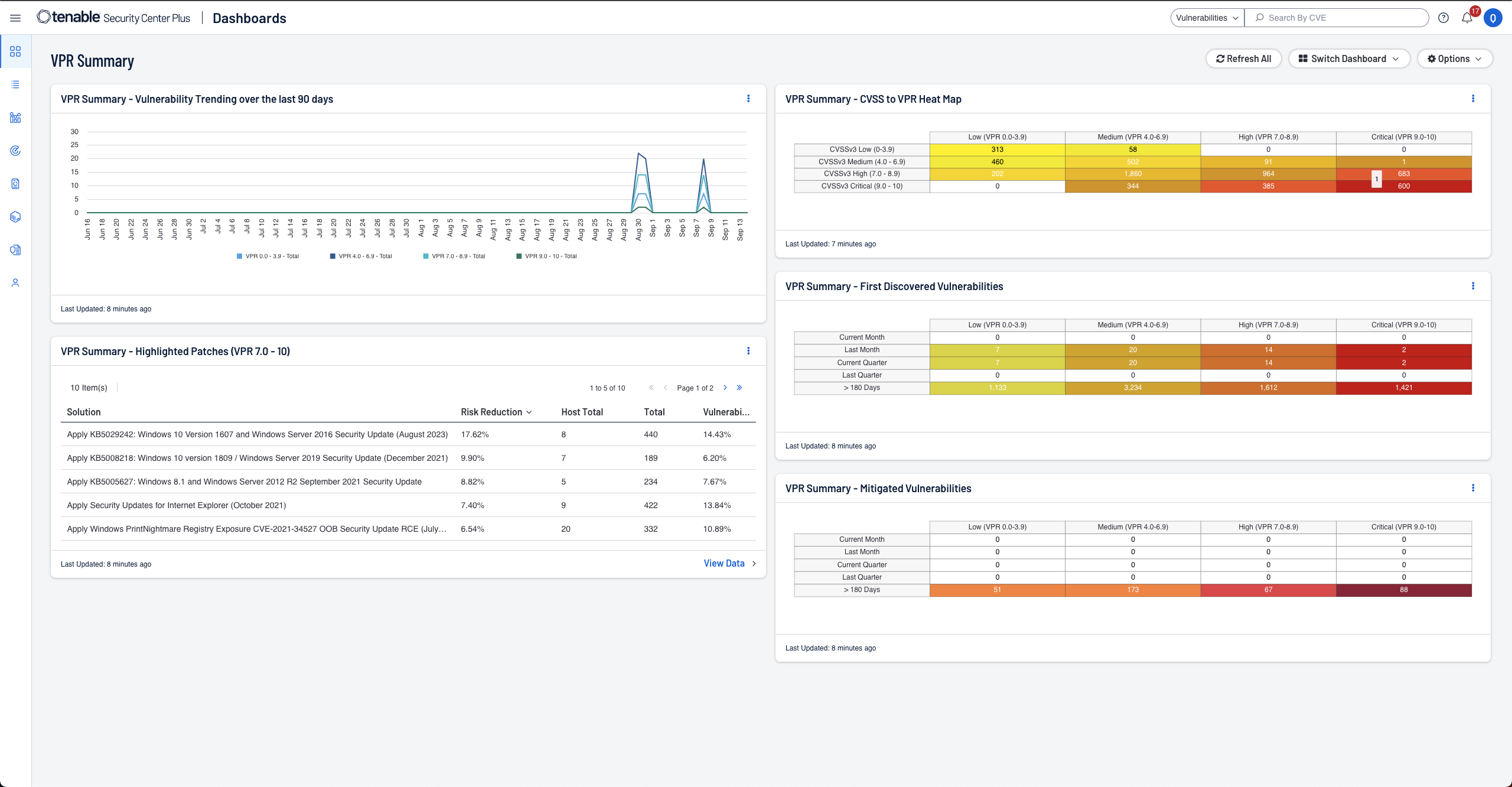

検出
アクティブスキャニング、エージェント、パッシブモニタリング、外部アタックサーフェス管理機能と CMDB との統合により、すべての資産が継続的に可視化できます。これには、利用開始までは存在が知られていなかった資産も含まれます。

評価
79,000 件を超える脆弱性をカバーする Tenable は、業界で最も広範囲にわたる CVE とセキュリティ構成をサポートしています。セキュリティとコンプライアンス体制をしっかりと理解することができます。

優先順位づけ
Tenable の予測に基づいた優先順位付けテクノロジーが、脆弱性データ、脅威インテリジェンス、データサイエンスを組み合わせて理解しやすいリスクスコアを算出します。最初に修正すべき脆弱性を把握することができます。
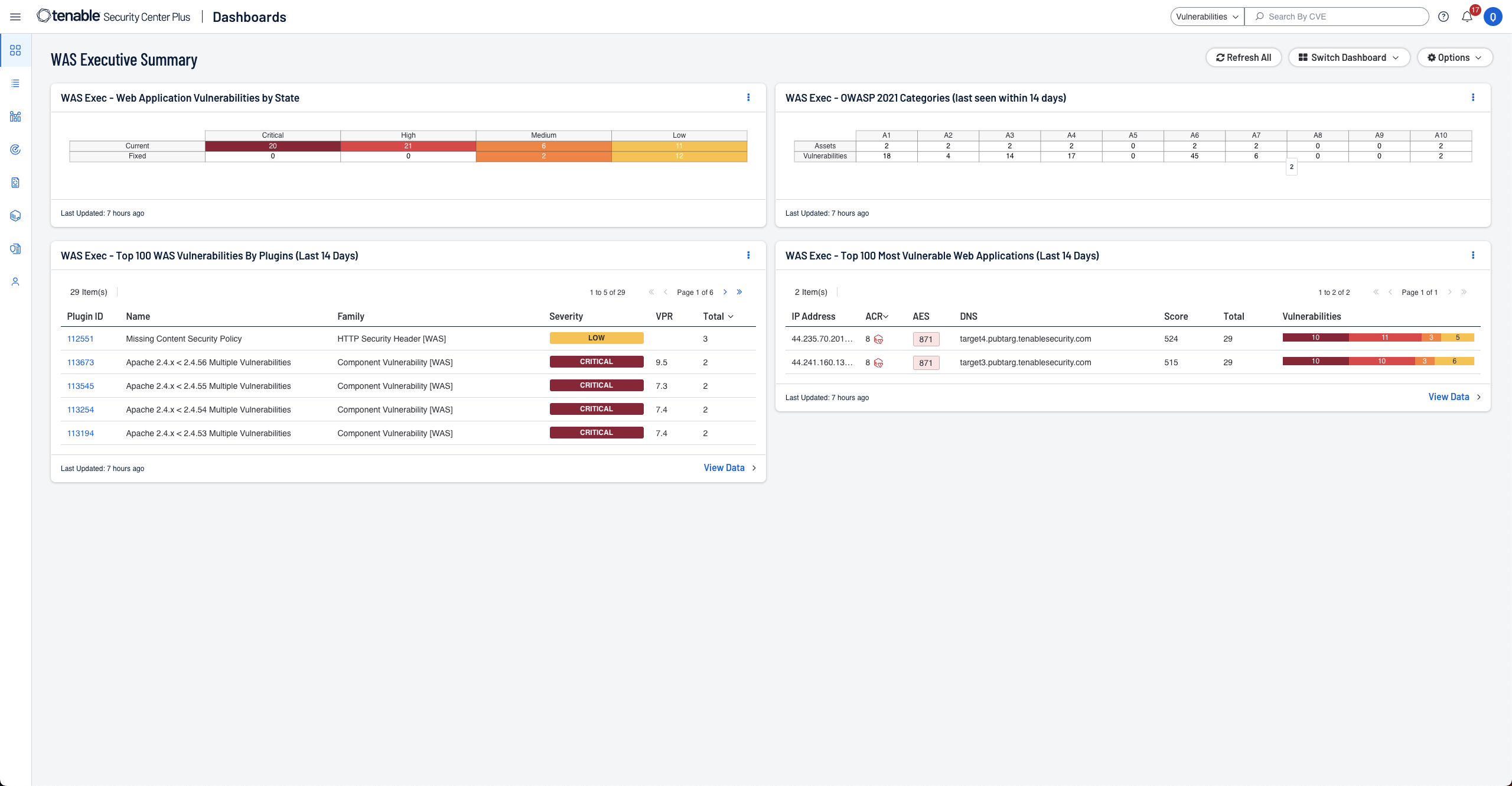
Tenable Security Center を通じてオンプレミスのウェブアプリケーションスキャンが利用可能
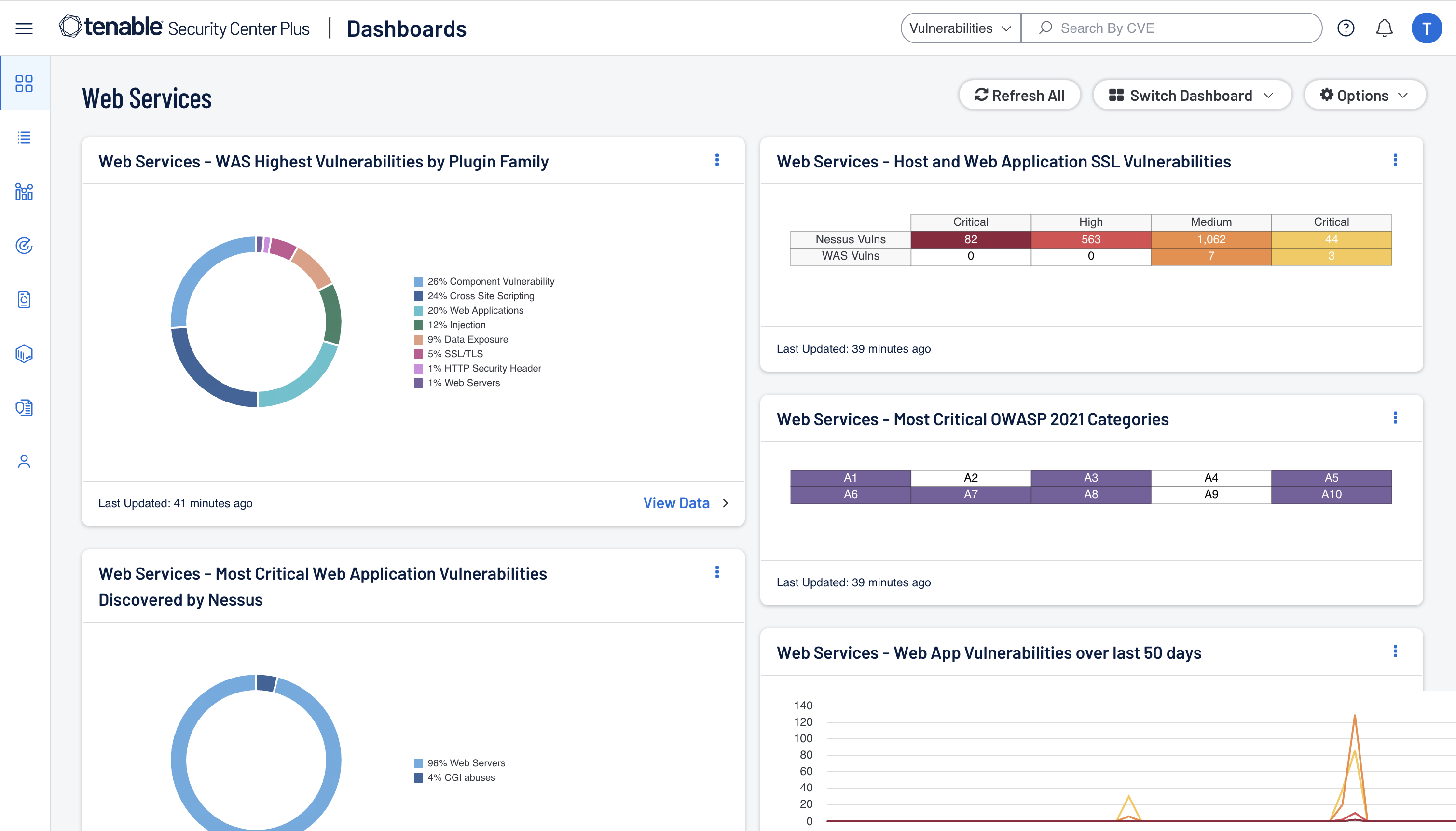
Tenable Web App Scanning を使用してオンプレミスウェブアプリケーションのセキュリティ対策を行うことで、防御を強化します。Security Center の UI にシームレスに統合された Tenable Web App Scanning により、ネットワークやウェブアプリケーション全体の脆弱性を特定して対処できるようになり、オンサイトでデータを管理しながらセキュリティ態勢の強化が可能です。
詳細はこちらからTenable.io は、Tenable One サイバーエクスポージャー管理プラットフォームに内蔵されています
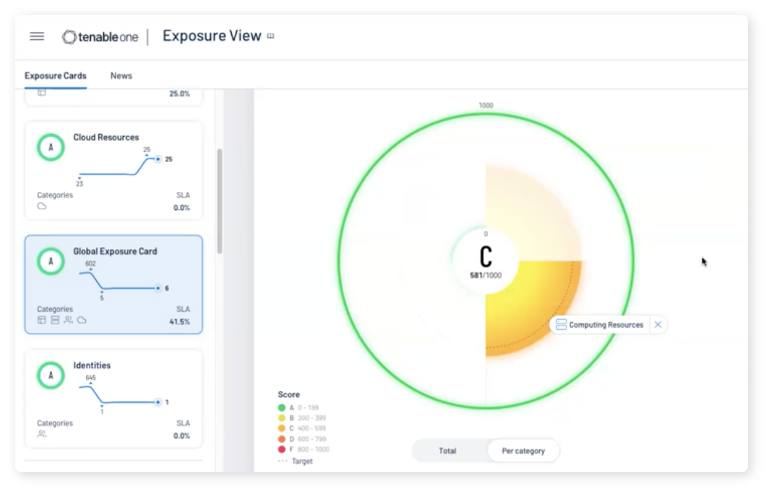
Tenable One は、DX 時代のアタックサーフェス全体を可視化して、可能性のある攻撃を防止し、サイバーリスクについて正確に伝達して最適なビジネスパフォーマンスを促進する、サイバーエクスポージャー管理プラットフォームです。 Tenable One プラットフォームは、IT 資産、クラウドリソース、コンテナ、ウェブアプリケーション、ID システムにわたる、高い網羅性を誇る脆弱性カバレッジを提供します。
詳細はこちらTenable Security Center のファミリー製品
Tenable Security Center
- リスクベースの脆弱性管理、オンプレミス
- 無制限の Nessus スキャナーでネットワークを即座に可視化
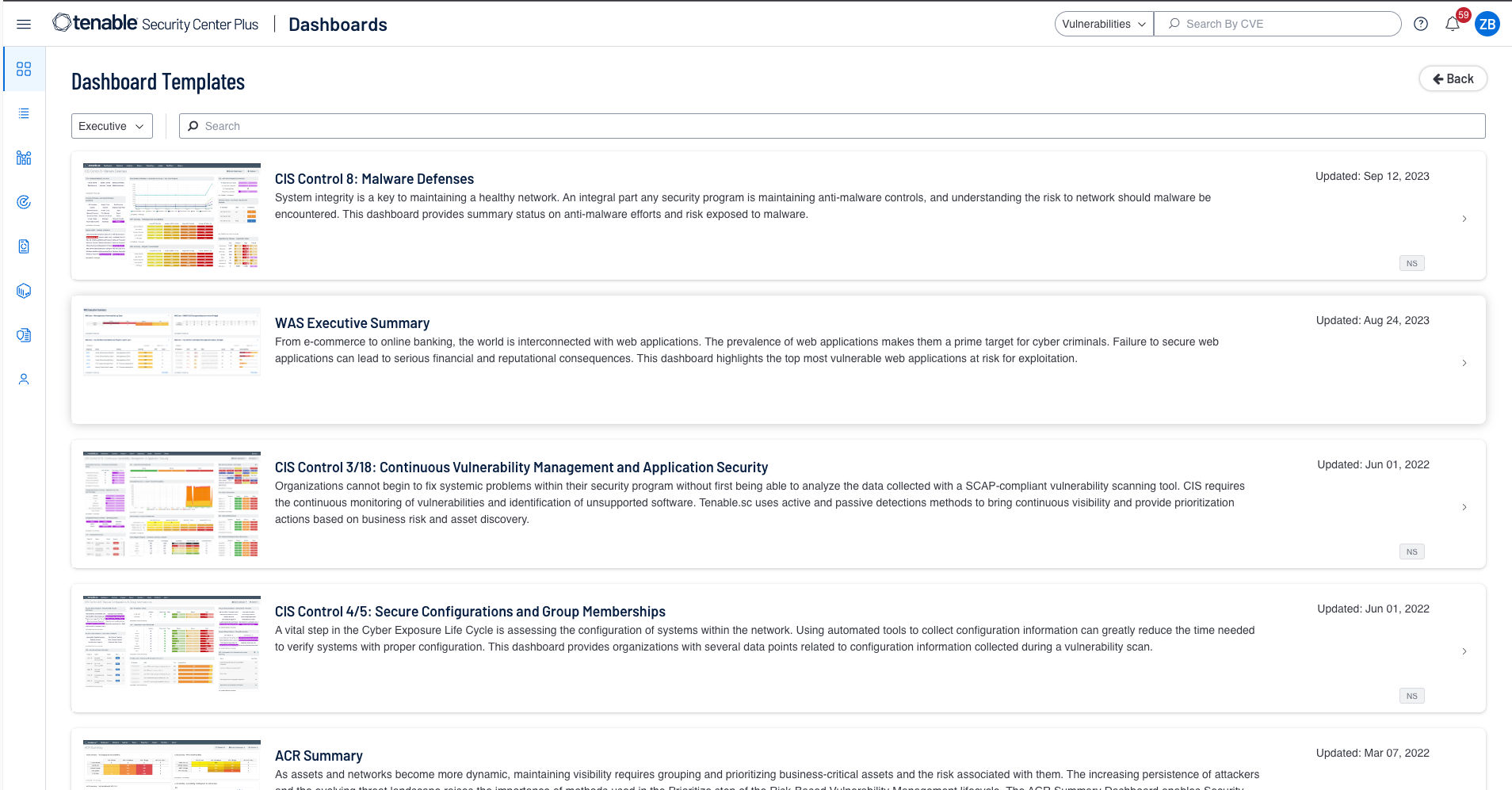
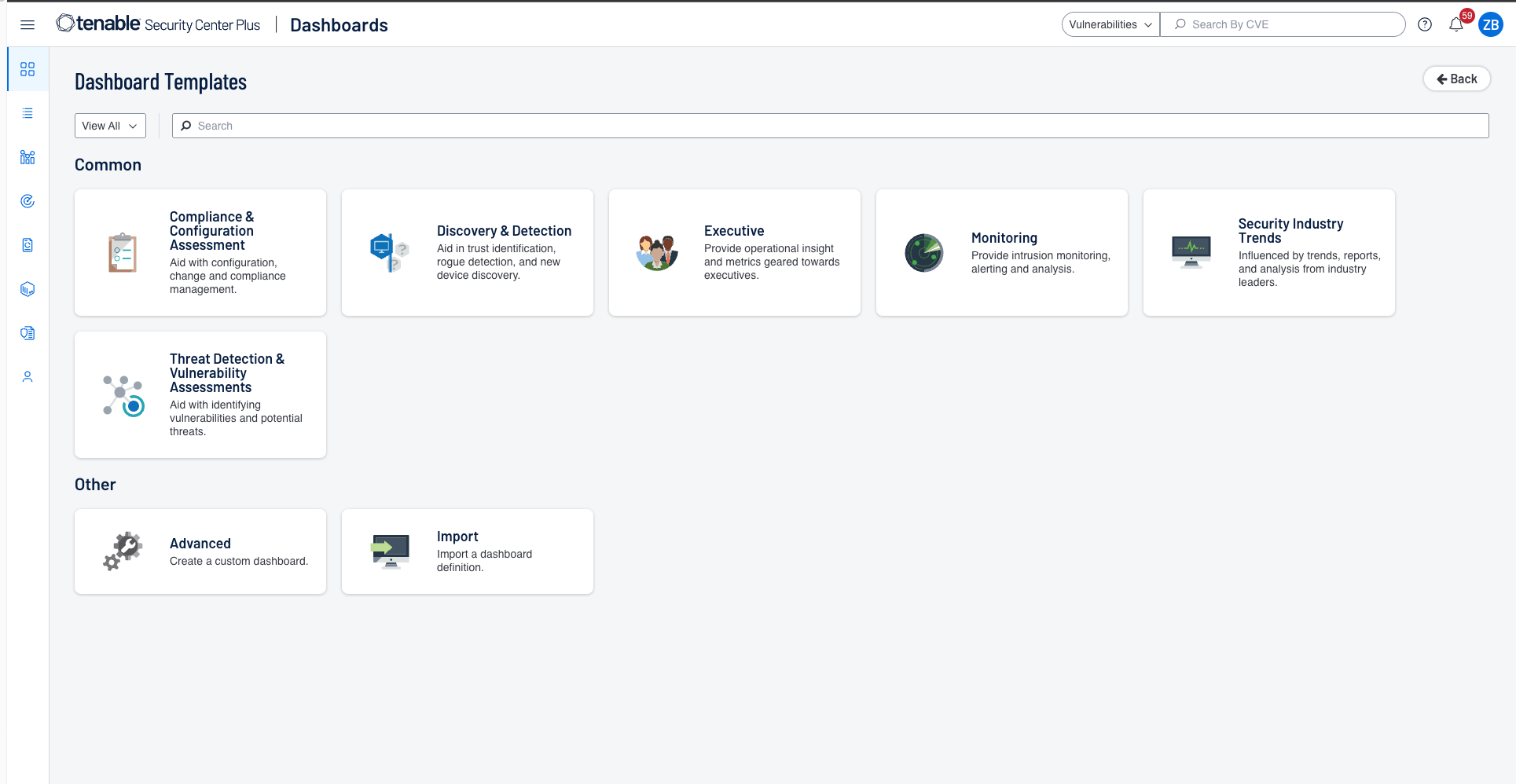
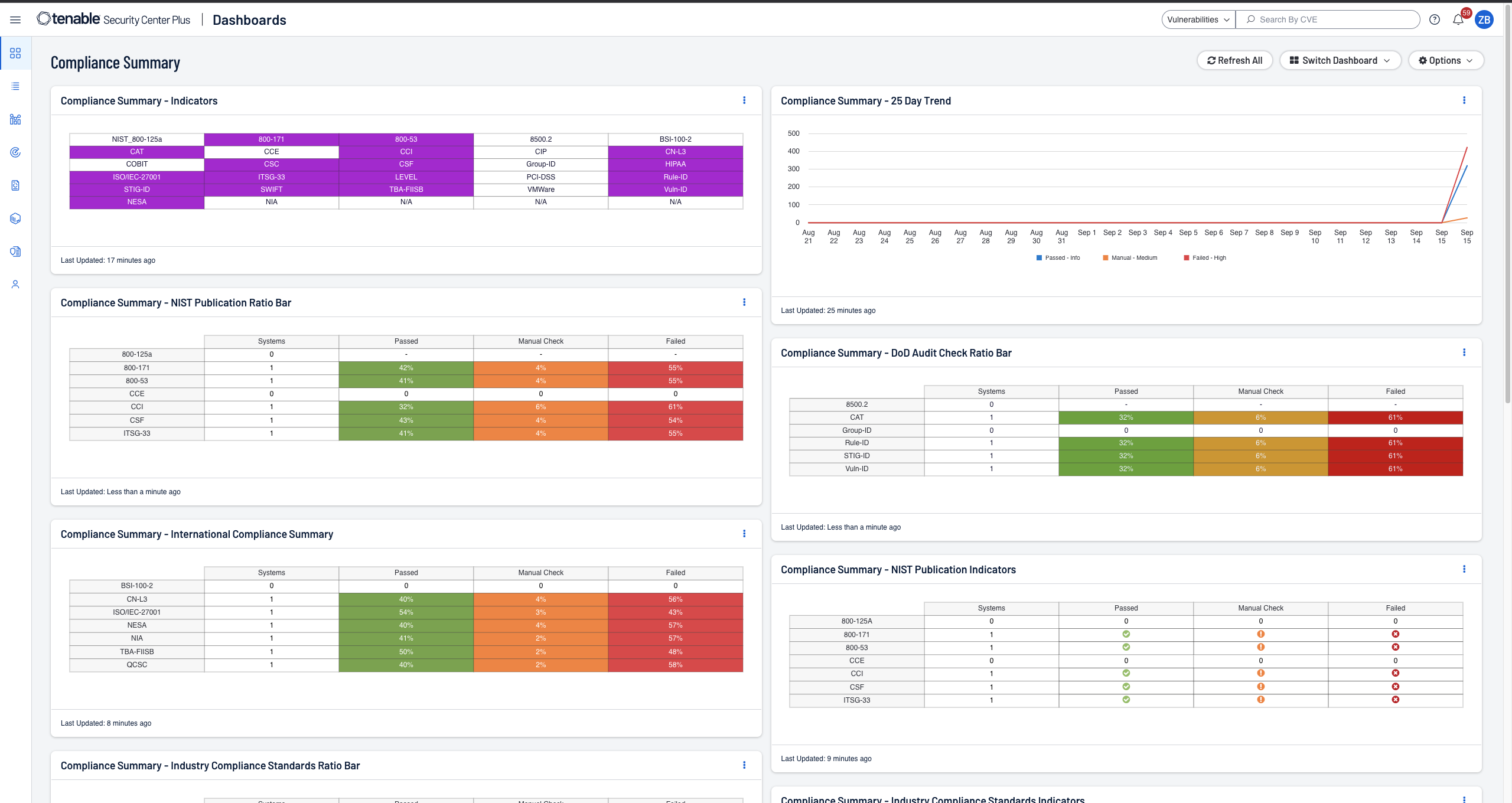
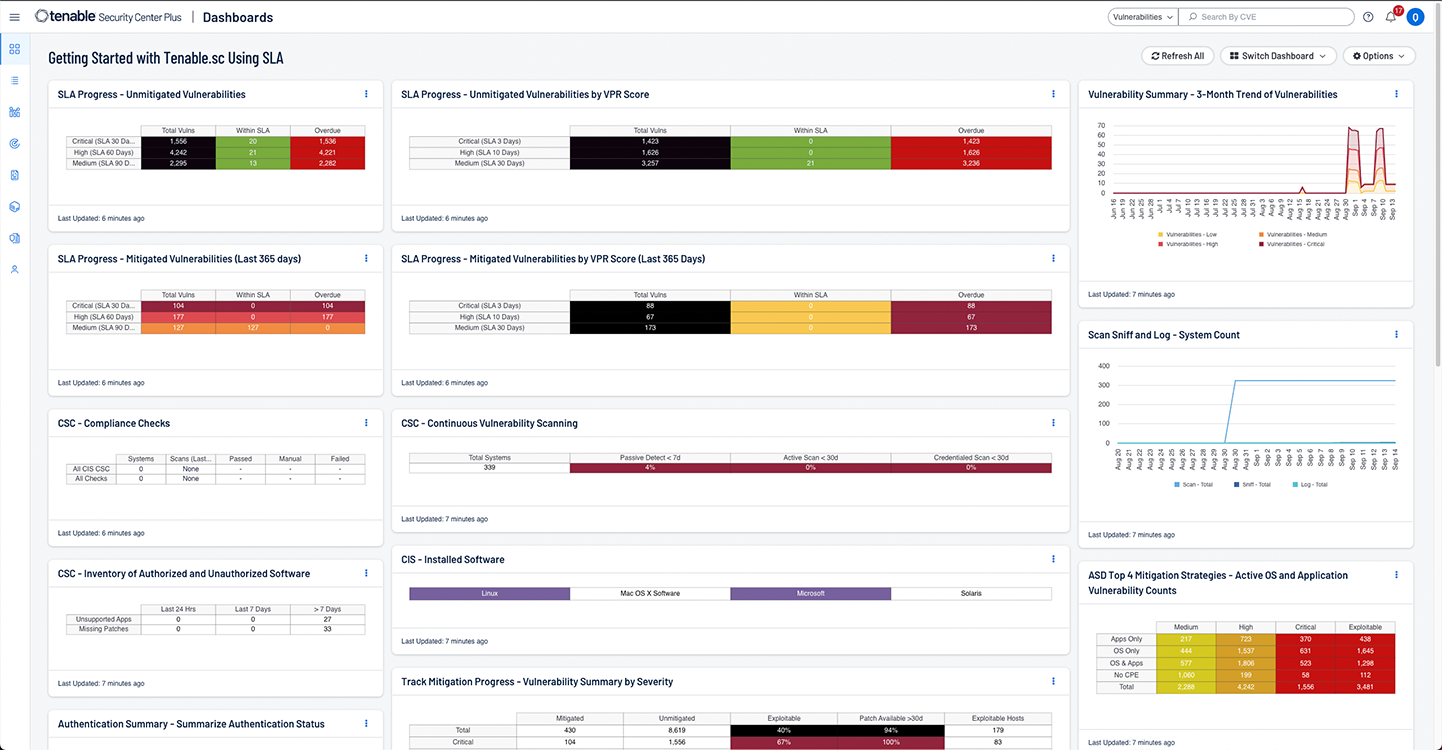
- 高度にカスタマイズ可能なダッシュボード、レポート、ワークフローを備え、データを明瞭で実行可能なインサイトに変えて提示
- 作り込みのリスクスコアと脅威インテリジェンスで脆弱性を即座に識別、優先順位付け
- カスタマイズ可能な構成アラート、通知、チケッティングにより、インシデント対応をスピードアップ
- クライアント統合、データ収集、データのエンリッチ化のための無料 API
- 今まで確認できなかった外部アタックサーフェス上の資産の検出
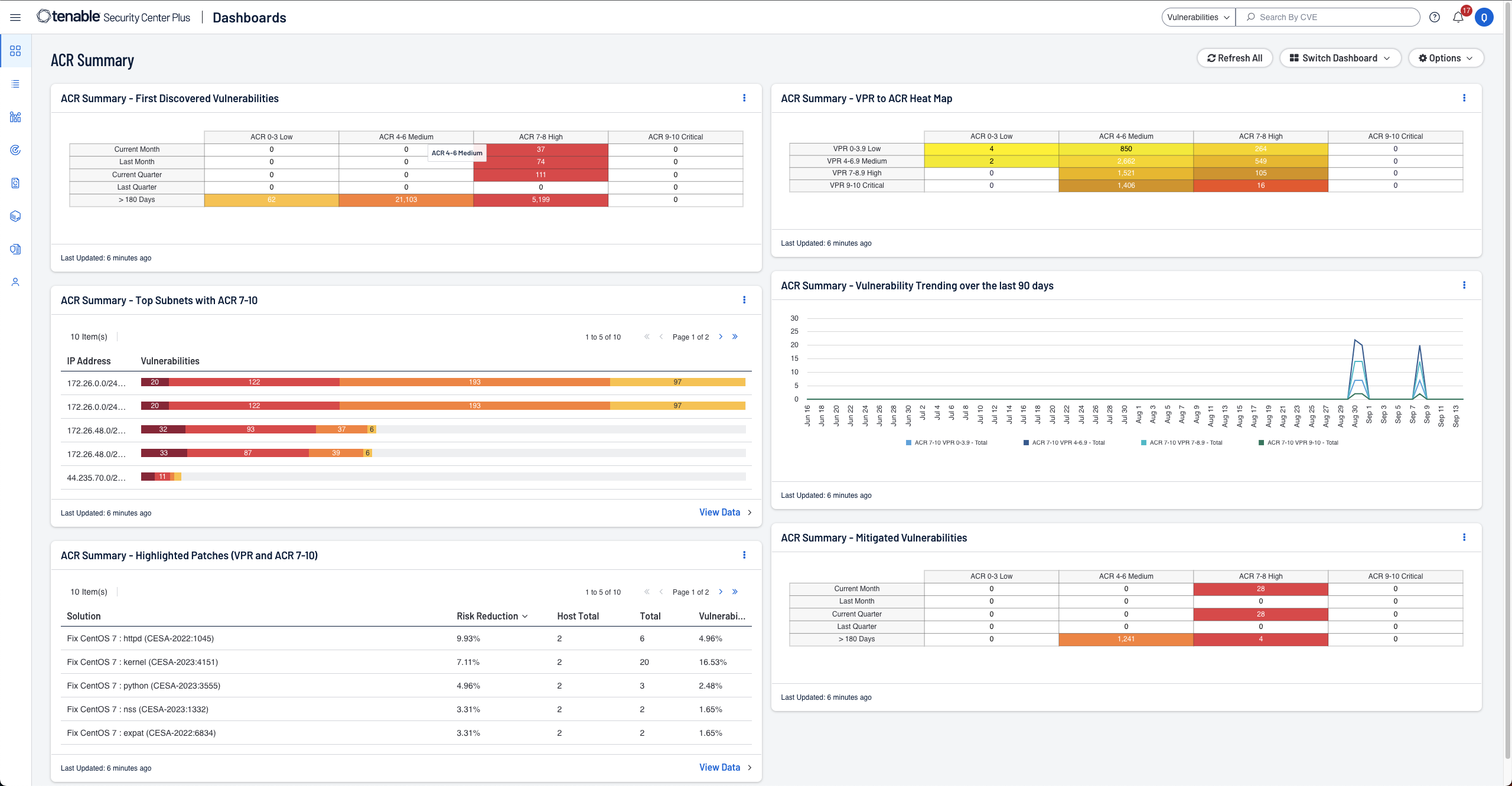
Tenable Security Center Plus
Tenable Security Center のすべての機能に加えて、以下が含まれます。
- Asset Criticality Rating (ACR) により資産をより深く理解してコンテキストを把握
- リアルタイムで資産や脆弱性を検出し、最高レベルの可視性を実現する継続的モニタリング
- リアルタイムメトリクスや違反に対する事前アラートで合理化されたコンプライアンス報告
- ボットネットおよびリモートトラフィックのリアルタイム検出
- これまで知られていないリソース、挙動変化、新しいアプリケーションの使用方法を洗い出す
Tenable Security Center Director
複数の Tenable Security Center コンソールをお持ちのお客様は、Tenable Security Center Director を Tenable Security Center または Tenable Security Center Plus のアドオンとして利用できます。
- すべての Tenable Security Center コンソールにまたがるネットワークを単一の画面で表示および管理が可能
- 各 Tenable Security Center コンソールのスキャンを 1 か所から簡単に管理
- レポーティングや、複数のコンソール、スキャナーおよび資産の管理を容易にできるよう、ネットワークを一元管理
- 複数の Tenable Security Center コンソールからのレポートが一元化され、サイバーリスクを簡単に測定可能
業界をリードする脆弱性管理
脆弱性管理ソリューションで脆弱性を特定、調査し、対策の優先付けをします
予測に基づいた優先順位付けで評価すると、優先的に修正すべき脆弱性の数が 97% 減ります。
「Tenable Security Center は、当社のネットワークにおける現状を正しく伝えてくれます。より深い知見を得られるので、責任を持ってセキュリティプログラムがうまくいっているのかどうかを検証できます」キャッツキルハドソン銀行、上級副社長兼テクノロジー部門主任 Ted Tomita 氏
セキュリティ面およびコンプライアンス面のリスクを高速で測定・分析
組織全体のサイバーリスクの管理と軽減を行う準備はできていますか?
Tenable Lumin が Tenable Security Center で利用できるようになりました。
Tenable Lumin の詳細はこちら