Web services that are vulnerable and not compliant with organizational policy based on current accepted standards present great risks to an organization, including the threats of network intrusion and data disclosure. The Web Services Assurance Report Card (ARC) presents policy statements that make use of vulnerability data and audit results to highlight issues with web services. The Open Web Application Security Project (OWASP) publishes a Top Ten list of critical web application security flaws, such as injection, broken authentication, and cross-site scripting (XSS). The policy statements in this ARC make reference to these flaws and can assist in measuring compliance with organizational policy for addressing web service vulnerabilities. This information will allow the Compliance Manager to continuously monitor policy compliance for web services, so that weak policies and weak policy enforcement can be identified and corrected and the network made more secure.
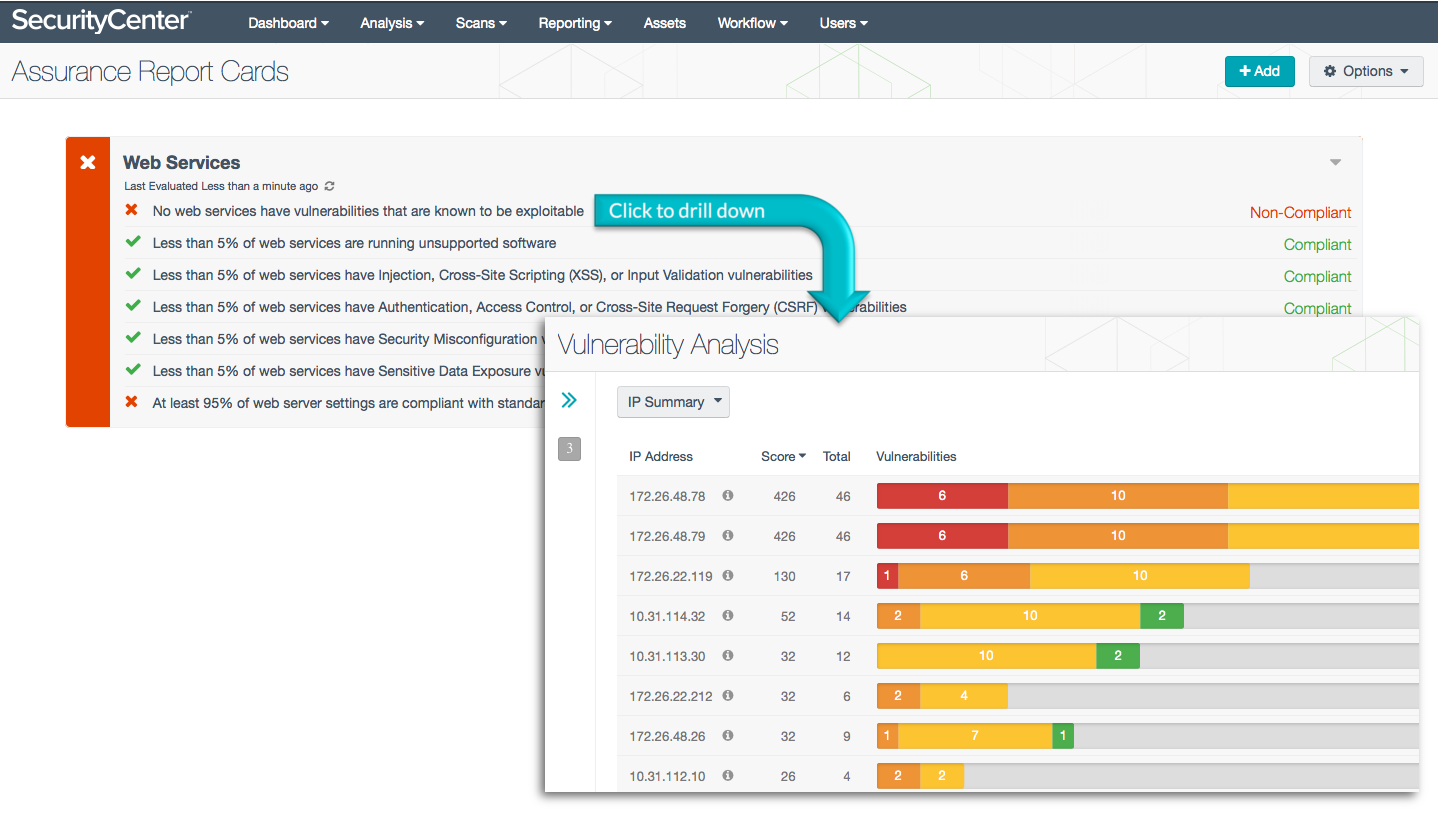
More details on each of the policy statements included in the ARC are given below. The Compliance Manager can click on a policy statement to bring up the analysis screen to display details on any compliance failures related to that policy statement. In the analysis screen, setting the tool to IP Summary will display the systems on which the compliance failures are present.
This ARC relies both on audit results obtained from Nessus scans of the systems on the network using appropriate audit files, and on vulnerability information collected by Nessus and PVS. The descriptions of the policy statements below include information on what details are used to find those checks relevant to the policy statement and what the percentage pass rate must be to be considered compliant. The audit files and ARC policy statement parameters are guides that can be customized as necessary to meet organizational requirements. If necessary, additional web application assets can be added in the Base and Drilldown filters of the ARC policy statements.
This ARC is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The ARC can be easily located in the Feed under the category Compliance. The ARC requirements are:
- SecurityCenter 5.0.0.1
- Compliance data
- Nessus 6.3.6
- PVS 4.2.1
Tenable's SecurityCenter Continuous View (SecurityCenter CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with Tenable's Passive Vulnerability Scanner (PVS), as well as log correlation with Tenable's Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network, in order to best measure compliance against complex standards.
ARC Policy Statements:
No web services have vulnerabilities that are known to be exploitable - This policy statement displays Compliant in green if none of the systems running web services have vulnerabilities that are known to be exploitable. Note that this policy statement is based only on vulnerabilities of the web services themselves; the machines running the web services may also be vulnerable. To secure the web services and meet compliance requirements, known exploitable vulnerabilities must be patched as soon as possible. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaw A9 (Using Components with Known Vulnerabilities).
Less than 5% of web services are running unsupported software - This policy statement displays Compliant in green if less than 5% of the systems running web services are running unsupported software. Note that this policy statement is based only on vulnerabilities of the web services themselves; the machines running the web services may also be vulnerable. To secure the web services and meet compliance requirements, versions of software that are no longer supported should be updated as soon as possible. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaw A9 (Using Components with Known Vulnerabilities).
Less than 5% of web services have Injection, Cross-Site Scripting (XSS), or Input Validation vulnerabilities - This policy statement displays Compliant in green if less than 5% of the systems running web services have injection, cross-site scripting (XSS), or other input validation vulnerabilities. Note that this policy statement is based only on vulnerabilities of the web services themselves; the machines running the web services may also be vulnerable. To secure the web services and meet compliance requirements, input validation vulnerabilities must be addressed as soon as possible. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaws A1 (Injection) and A3 (Cross-Site Scripting).
Less than 5% of web services have Authentication, Access Control, or Cross-Site Request Forgery (CSRF) vulnerabilities - This policy statement displays Compliant in green if less than 5% of the systems running web services have authentication, access control, cross-site request forgery (CSRF), or other related vulnerabilities. Note that this policy statement is based only on vulnerabilities of the web services themselves; the machines running the web services may also be vulnerable. To secure the web services and meet compliance requirements, authentication and access control vulnerabilities must be addressed as soon as possible. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaws A2 (Broken Authentication and Session Management), A4 (Insecure Direct Object References), A7 (Missing Function Level Access Control), A8 (Cross-Site Request Forgery), and A10 (Unvalidated Redirects and Forwards).
Less than 5% of web services have Security Misconfiguration vulnerabilities - This policy statement displays Compliant in green if less than 5% of the systems running web services have security misconfiguration vulnerabilities. Note that this policy statement is based only on vulnerabilities of the web services themselves; the machines running the web services may also be vulnerable. To secure the web services and meet compliance requirements, security misconfiguration vulnerabilities must be addressed as soon as possible. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaw A5 (Security Misconfiguration).
Less than 5% of web services have Sensitive Data Exposure vulnerabilities - This policy statement displays Compliant in green if less than 5% of the systems running web services have sensitive data exposure vulnerabilities. Note that this policy statement is based only on vulnerabilities of the web services themselves; the machines running the web services may also be vulnerable. To secure the web services and meet compliance requirements, sensitive data exposure vulnerabilities must be addressed as soon as possible. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaw A6 (Sensitive Data Exposure).
At least 95% of web server settings are compliant with standards and policies - This policy statement displays Compliant in green if at least 95% of the compliance checks on web server settings have passed. Web server compliance checks are identified by text strings such as "Apache", "IIS", or "Application server" in their descriptions. If necessary, additional text strings can be added in the Base and Drilldown filters of this policy statement. To secure web services and meet compliance requirements, non-compliant web server settings must be addressed. This policy statement can assist in addressing the OWASP Top Ten for 2013, security flaw A5 (Security Misconfiguration).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success