by Steve Tilson
June 22, 2017
Detecting unusual or anomalous network behavior is impossible without first establishing a baseline of network activity for comparison. Tenable NetFlow Monitor is a powerful tool for developing an audit trail of what has happened within a network. This report leverages NetFlow statistics collected by Tenable Log Correlation Engine (LCE) to provide a network traffic baseline or a comparison.
NetFlow is a network protocol used to collect and monitor information from network traffic. Tenable NetFlow Monitor (TFM) is a powerful tool that can assist in creating an overview of network activity. Routers and switches that support NetFlow can collect IP traffic statistics on all interfaces where NetFlow is enabled. The TFM client takes advantage of the ability in most modern routers to use the NetFlow protocol to send network session statistics. The network devices or the TFM then export the statistics as NetFlow TFM records to LCE that includes information on ports, source and destination IP addresses. This enables you to monitor network traffic without having to install a sniffer on a hub or switched span port. Also, Tenable NetFlow Monitor possesses de-duplication logic to eliminate duplicate flow records from different sources.
A healthy network is critical to all organizations and administrators should monitor and maintain an efficient network. Being able to identify hosts that are creating or receiving traffic, whether authorized or unauthorized, assists administrators in making decisions about prioritization of resources and necessary changes to the network. Analysis of data gathered by TFM may help administrators identify misconfigured devices, data exfiltration, scans from outside sources, denial of service attacks and compromised hosts. In addition to issues listed, unchecked traffic can create issues for organizations by consuming valuable bandwidth unnecessarily. Network administrators can also use this information for network expansion analysis by monitoring subnet traffic.
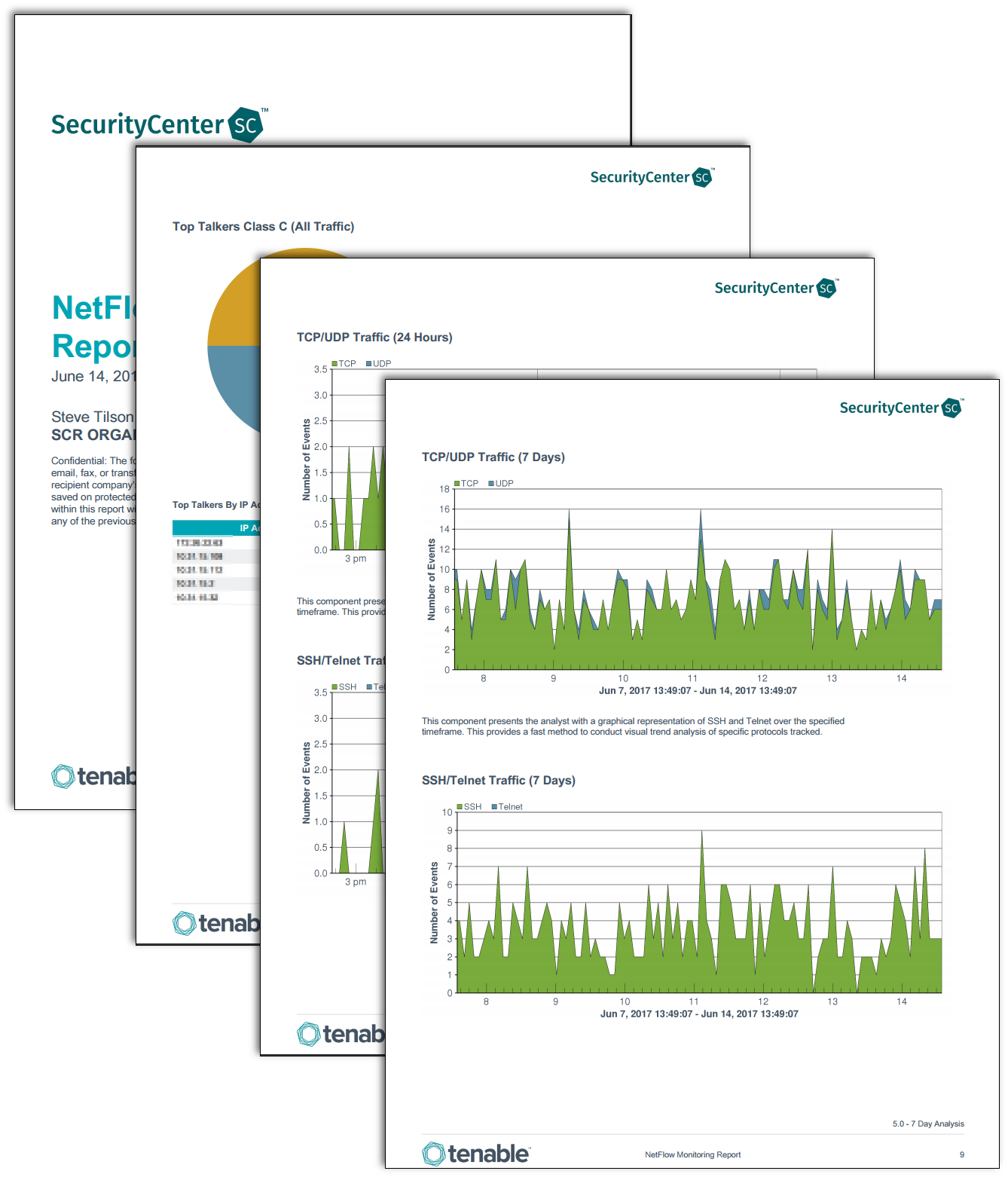
Network administrators benefit from NetFlow monitoring and analysis report by analyzing the traffic collected in LCE from the TFM client, and provides complete visibility into network traffic flow and volume. This report displays event statistics leveraging the capabilities of TFM Normalized Events. This event data is correlated to produce a series of pie charts and area chart lines to display statistical data. Administrators can use this report to consistently monitor network traffic and to analyze the health of the network once a baseline is obtained.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 5.4.5
- LCE 5.0.1
- Tenable NetFlow Monitor
Tenable SecurityCenter Continuous View (SecurityCenter CV) provides continuous network monitoring, vulnerability identification and security monitoring. SecurityCenter CV is continuously updated with information about advanced threats, zero-day vulnerabilities and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, and enabling decisive action that transforms a security program from reactive to proactive. Leveraging Tenable LCE, as well as the NetFlow Monitor and Network Monitor clients provide analysis for determining network efficiency and security. Tenable enables powerful, yet non-disruptive, continuous monitoring of the organization to ensure all events are monitored and captured for analysis of the network traffic.
The following chapters are included:
Top Talkers: The Top Talker chapter presents analysts with charts and tables leveraged by Tenable NetFlow Monitor for tracking the top hosts with the most network traffic leveraged. The data displayed gives a starting point for identifying the most active hosts that may need further analyzing depending on the hosts role.
NetFlow Analysis Last Hour: The NetFlow Analysis Last Hour chapter presents further breakdown of identified data with charts and tables for a trend analysis over the last hour for http/https, tcp/udp and ssh/telnet protocols.
NetFlow Analysis for 24 Hours: The NetFlow Analysis Last Hour chapter presents further breakdown of identified data with charts and tables for a trend analysis over the last 24 hours for http/https, tcp/udp and ssh/telnet protocols.
NetFlow Analysis Last 7 Days: The NetFlow Analysis Last 7 Days chapter presents further breakdown of identified data with charts and tables for a trend analysis over the last hour for http/https, tcp/udp and ssh/telnet protocols.