Mr. Robot Cleaning House at E-Corp

The second episode of Mr. Robot finds Elliot starting his new job at E-Corp. As he joins his new team and is looking to find a way to delay the shipment of all the paper data to New York facility, Elliott runs into the normal corporate middle management delays. He quickly realizes his first obstacle, William the Technology Manager, is up to no good and is deploying Rootkits on phones and selling the personal data collected. To circumvent this first obstacle, Elliot breaks out a good tool called theHarvester, and then promptly calls the feds. Watch out Evil Corp, Elliot is cleaning house, while trying to delay the stage two attack.
theHarvester
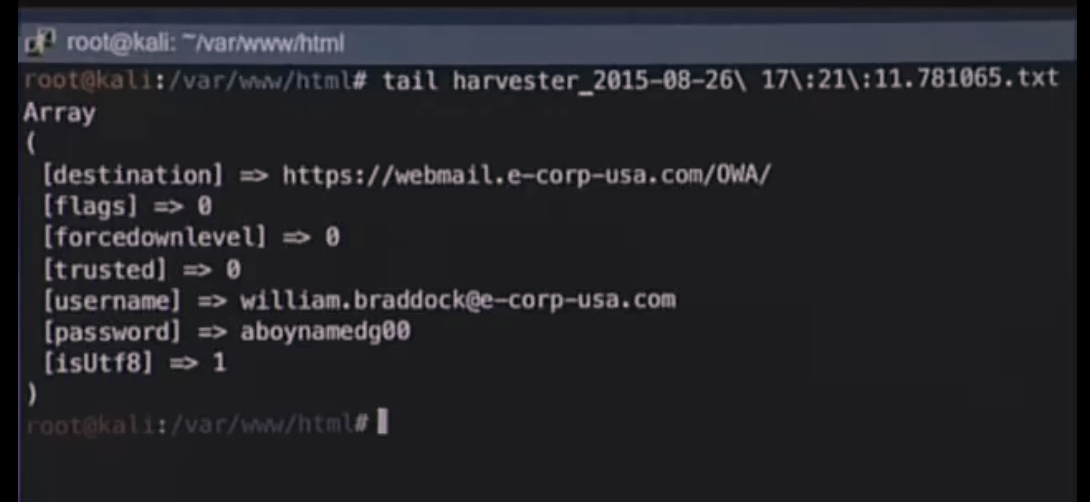
During a pentest, the security professionals go through a reconnaissance phase where data on the target is collected. Having used theHarvester a few times myself, I found that time spent collecting subdomains, email and SHODAN results helps to really understand vantage points into the target for exploitation. In this episode, Elliot uses the tail command to view the results of theHarvester and get his manager's password. He reads the email and identifies that his manager is using rootkits on the mobile devices. Elliot promptly notifies the feds. E-Corp may not be Evil for long.
Rootkits
Rootkits on mobile devices, laptops, servers and other types of assets are often hidden very well within the OS, thus making their discovery challenging, to say the least. Tenable.io™ has very advanced technology developed in a series of plugins to detect Malicious Processes, Malicious Content, Malicious File Detection and support for Yara. By using the plugins and Yara rules shown below, you can search your network for the rootkits or other malicious software.
- 52670|Web Site Links to Malicious Content
- 59275|Malicious Process Detection
- 59641|Malicious Process Detection: Potentially Unwanted Software
- 64687|Malicious Process Detection: APT1 Software Running
- 64788|Malicious Process Detection: Malware Signed By Stolen Bit9 Certificate
- 65548|Malicious Process Detection: User Defined Malware Running
- 71024|Web Site Hosting Malicious Binaries
- 71261|Linux Malicious Process Detection
- 71263|Mac OS X Malicious Process Detection
- 88958|Malicious File Detection: APT1 Software on System
- 88959|Malicious File Detection: Malware Signed By Stolen Bit9 Certificate
- 88960|Malicious File Detection: Invalid Directories
- 88961|Malicious File Detection
- 88962|Malicious File Detection: User Defined Malware
- 88963|Malicious File Detection: Potentially Unwanted Software
- 91223|Malicious Process Detection: User Defined Malware Running (Linux)
- 91224|Malicious Process Detection: User Defined Malware Running (Mac OS X)
- 91990|Malicious File Detection Using Yara
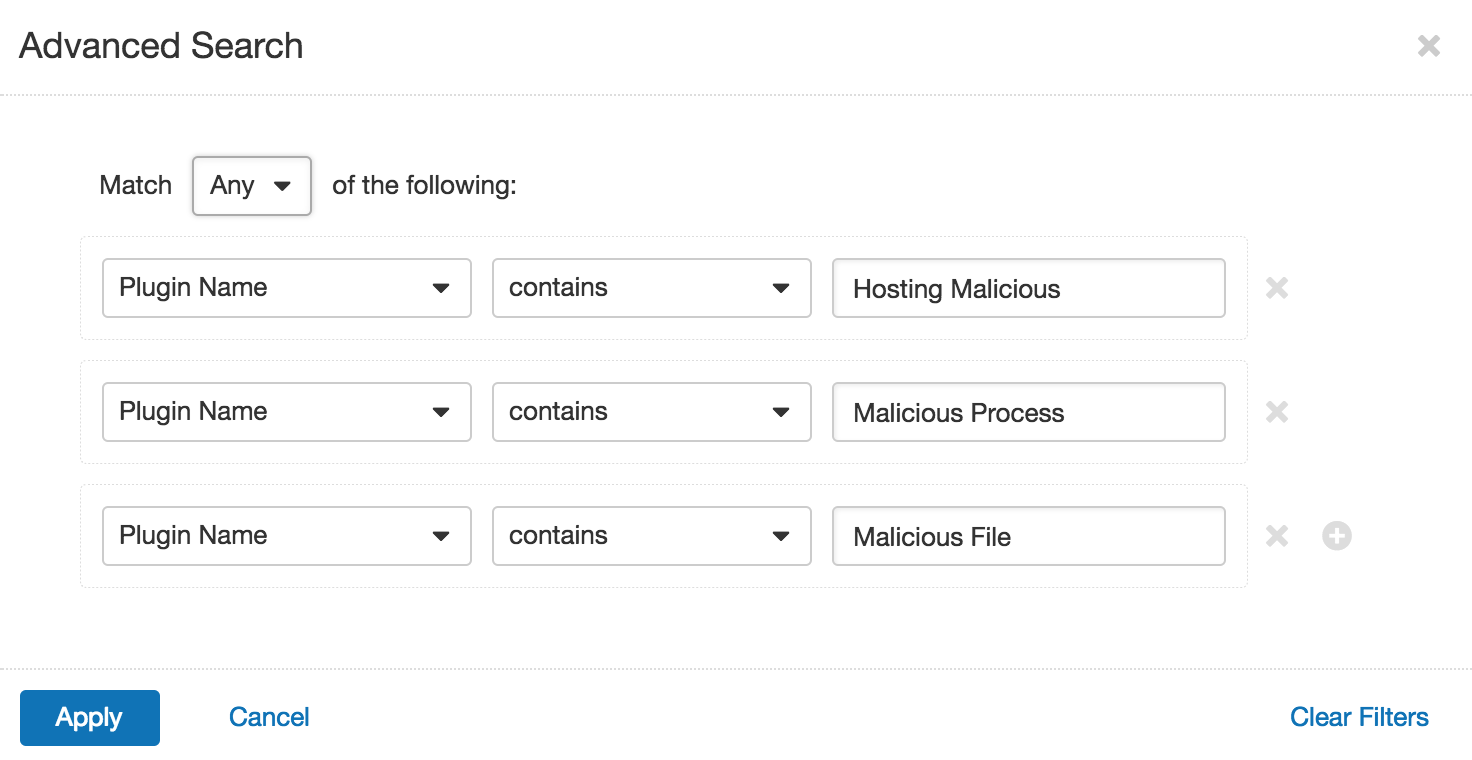
By searching for three terms “Malicious File, Malicious Process, and Hosting Malicious,” you can easily locate all the plugins which provide indications of rootkits in your network.
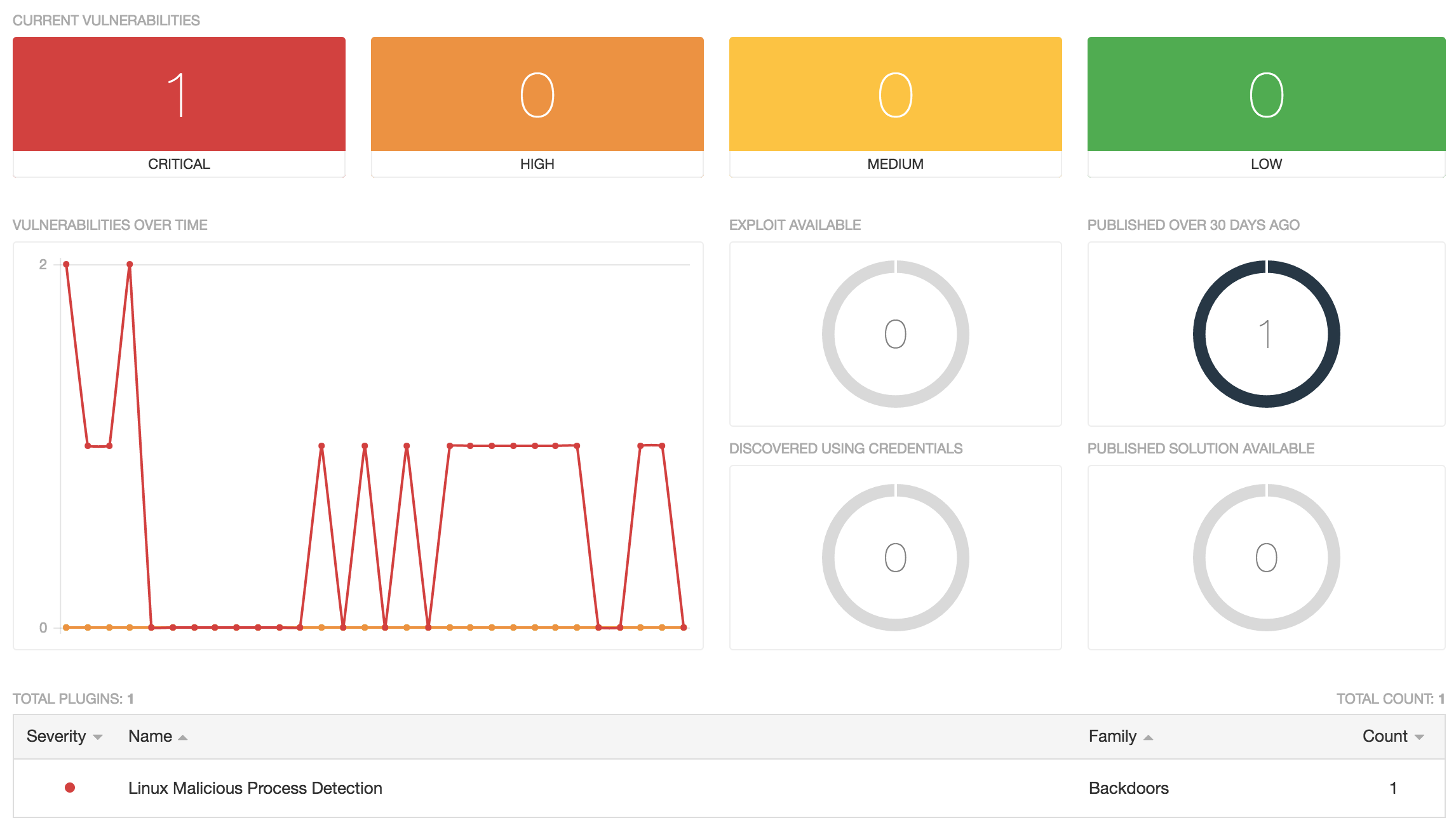
In my test data, you can see I have one system I need to investigate. The plugins will return files and URLs to help you better understand and defend against the malware or rootkit.
Modern Attack Surface
The detection of rootkits was difficult when confined to managed devices, but now that the modern IT landscape consists of web apps, containers, cloud instances and IoT, the ability to detect rootlets becomes even more challenging. Tenable.io is the first Cyber Exposure platform to provide you with holistic visibility across your modern attack surface, allowing you to detect rootkits or other malicious software on your network. Start a free 60-day trial of Tenable.io for your organization today.