On November 3rd, 2021, CISA issued Binding Operational Directive (BOD) 22-01, Reducing the Significant Risk of Known Exploited Vulnerabilities establishing a CISA managed catalog of known exploited vulnerabilities and requires federal civilian agencies to identify and remediate these vulnerabilities on their information systems. Tenable.sc allows organizations to quickly summarize and track specific vulnerabilities to ensure proper discovery and mitigation. This dashboard showcases progress in mitigation of these vulnerabilities to allow organizations to ensure a reduced attack surface.
The DHS says:
The United States faces persistent and increasingly sophisticated malicious cyber campaigns that threaten the public sector, the private sector, and ultimately the American people’s security and privacy. The federal government must improve its efforts to protect against these campaigns by ensuring the security of information technology assets across the federal enterprise. Vulnerabilities that have previously been used to exploit public and private organizations are a frequent attack vector for malicious cyber actors of all types. These vulnerabilities pose significant risk to agencies and the federal enterprise. Aggressively remediating known exploited vulnerabilities is essential to protect federal information systems and reduce cyber incidents.
Directive 22-01, Reducing the Significant Risk of Known Exploited Vulnerabilities establishes a CISA-managed catalog of known exploited vulnerabilities that carry significant risk to the federal enterprise and establishes requirements for agencies to remediate any such vulnerabilities included in the catalog. CISA will determine vulnerabilities warranting inclusion in the catalog based on reliable evidence that the exploit is being actively used to exploit public or private organizations by a threat actor. This directive enhances but does not replace BOD 19-02, which addresses remediation requirements for critical and high vulnerabilities on internet-facing federal information systems identified through CISA’s vulnerability scanning service.
The CISA Known Exploited Vulnerabilities Catalog defined the vulnerabilities to be address by November 17th, 2021 (BOD 22-01). Tenable.sc assists the CISO in identifying actions needed to mitigate these vulnerabilities along with others identified in past due advisories. The CVE’s tracked by CISA in this dashboard are subject to change and new dashboards will be provided as needed.
Tenable.sc uses active credentialed scanning and/or agent based scanning to collect information needed to identify known exploitable vulnerabilities. Allowing the risk manager to work with asset owners to establish an ongoing remediation action plan, which demonstrate compliance with this directive.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
- Tenable.sc 5.20.0
- Nessus 8.15.2
Risk-based vulnerability management (RBVM) is a process that reduces vulnerabilities across the agency's attack surface by prioritizing remediation actions to the risks CISA identifies. Tenable.sc enables the agency to go beyond just discovering vulnerabilities, and provides the life cycle steps to establish internal validation and enforcement procedures that demonstrate adherence with this Directive.
Components:
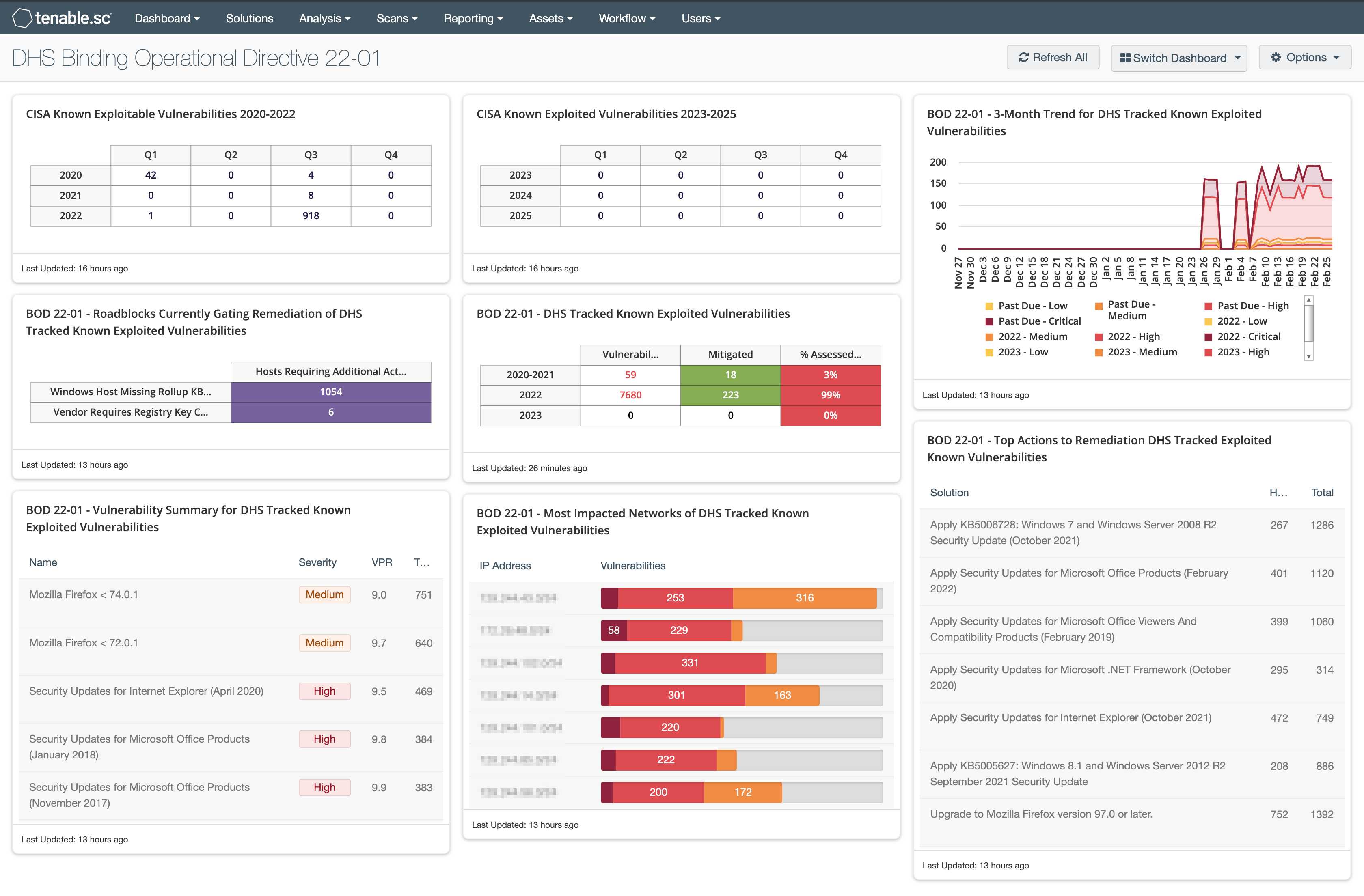
CISA Known Exploitable Vulnerabilities 2020-2022: The CISA Known Exploitable Vulnerabilities 2020-2022 matrix displays data by quarter for vulnerabilities that are, or may already be past due to be remediated. These dates are derived from the CISA Known Exploited Vulnerabilities Catalog. The element uses the Cross Reference filter to exactly match the filters included in the CISA Known Exploited Vulnerabilities Catalog.
CISA Known Exploited Vulnerabilities 2023-2025: The CISA Known Exploitable Vulnerabilities 2023-2025 matrix displays data by quarter for vulnerabilities that will become due to be remediated by a specific date. These dates are derived from the CISA Known Exploited Vulnerabilities Catalog. The element uses the Cross Reference filter to exactly match the filters included in the CISA Known Exploited Vulnerabilities Catalog.
BOD 22-01 - 3-Month Trend for DHS Tracked Known Exploited Vulnerabilities: This chart displays an area trend chart of vulnerabilities related to DHS Binding Operational Directive 22-01. The vulnerabilities displayed reflect those that are already past due and those due Nov 17th, 2021.
BOD 22-01 - Vulnerability Summary for DHS Tracked Known Exploited Vulnerabilities: This table displays vulnerabilities sorted by total and shows the name, severity, VPR score, and total vulnerability counts for vulnerabilities past due and due Nov 17th, 2021.
BOD 22-01 - DHS Tracked Known Exploited Vulnerabilities: This matrix displays vulnerability status counts on past due vulnerabilities, vulnerabilities due Nov 17th 2021, and vulnerabilities due May 3rd 2021. The vulnerability column displays the vulnerability count and is followed by the mitigated vulnerability count and percentage of vulnerable hosts.
BOD 22-01 - Roadblocks Currently Gating Remediation of DHS Tracked Known Exploited Vulnerabilities: This matrix displays known/identified roadblocks to completing remediation efforts. The component uses the CVE filter to exactly match the filters included in the CISA Known Exploited Vulnerabilities Catalog. This component also filters through the vulnerability text to determine whether a host is missing a Rollup KB or contains a registry key.
BOD 22-01 - Most Impacted Networks of DHS Tracked Known Exploited Vulnerabilities: This component displays the most impacted class C Networks based on the number of detected vulnerabilities that are past due or due Nov 17th 2021.
BOD 22-01 - Top Actions to Remediation DHS Tracked Exploited Known Vulnerabilities: This component displays a table sorted by Risk Reduction that shows solutions, host count and vulnerability count for vulnerabilities past due and due Nov 17th 2021.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success