by Carole Fennelly
June 24, 2022
Organizations that handle sensitive data, such as healthcare and credit card information, are required to audit data protection controls on an annual basis. Leveraging Tenable dashboards enables organizations to protect data in accordance with business risk posture for Confidentiality, Integrity and Availability (CIA).
The National Institute of Standards (NIST) Special Publication 800-53 provides comprehensive guidance for a secure infrastructure, including guidance on data protection and encryption. The information provided in Tenable dashboards and reports enables Risk Managers and Chief Privacy Officers to demonstrate to third parties and regulatory bodies that sensitive data is protected in accordance with Data Loss Prevention requirements.
The NIST Cybersecurity Framework (CSF) is a control framework, which has high level controls that align with ISO 27001, NIST SP 800-53, and others. The Cybersecurity Framework’s prioritized, flexible, and cost-effective approach helps to promote the protection and resilience of critical infrastructure and other sectors important to the economy and national security. Many regulating bodies accept evidence documentation of compliance with the NIST CSF as assurance that the organization has effective controls in place to meet security requirements. The HIPAA Security Rule Crosswalk to NIST Cybersecurity Framework is an example of a regulation aligning with NIST.
The dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard is located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
Tenable.sc 5.9.0
Nessus 10.2.0
Leveraging Tenable dashboards enables operations teams to verify that appropriate protections are in place for data at rest, data in transit, and removable media. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives.
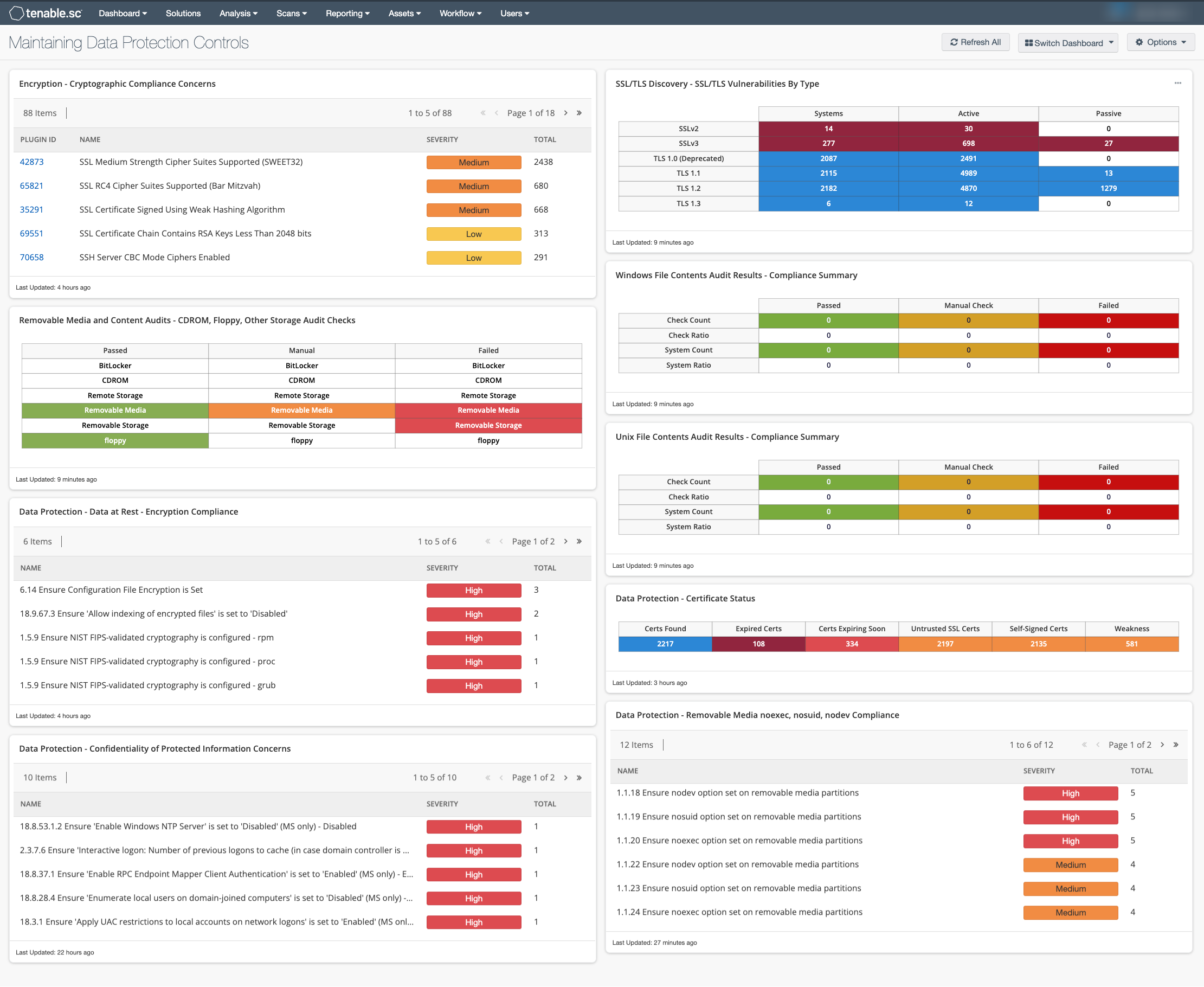
Components
Encryption – This table presents a summary of both compliance concerns and vulnerabilities associated with encryption and cryptographic issues. Information presented in this component can highlight issues such as weak hashing algorithms and keys as well as the use of insecure encryption ciphers, including SSLv2, SSLv3, and TLSv1.0.
Removable Media and Content Audits - CDROM, Floppy, Other Storage Audit Checks – This component focuses on compliance data, filtering on strings containing CDROM, floppy, and other removable storage devices in the plugin name. When an audit file is imported into SecurityCenter the 'description' line for the check becomes the plugin name.
SSL/TLS Discovery - SSL/TLS Vulnerabilities By Type: This component provides an overview of systems and vulnerabilities related to SSL/TLS. Separating the view based on detection method and SSL/TLS version, enables analysts to ensure that all SSL/TLS related PCI security issues are identified and can be mitigated.
Windows File Contents Audit Results - Compliance Summary: This component provides an overview of systems and vulnerabilities related to SSL/TLS. Security analysts can benefit from a summary view of the data set when performing configuration audit of systems in accordance with a Governance Risk and Compliance (GRC) program. The Windows File Contents Compliance Summary matrix provides a high-level view of the Windows File Contents compliance status.
Unix File Contents Audit Results - Compliance Summary: The Unix File Contents Compliance Summary matrix provides a high-level view of the Unix File Contents compliance status. Security analysts can benefit from a summary view of the data set when performing configuration audit of systems in accordance with a Governance Risk and Compliance (GRC)program. The Unix File Contents Compliance Summary table provides a high-level view of the Unix File Contents compliance status.
Data Protection - Data at Rest - Encryption Compliance: This table displays findings related to Security Requirement 3.13.16 in the NIST Special Publication 800-171 Revision 2. The table displays the Plugin Name, Severity, and Total, sorted by the total number of vulnerabilities identified.
Data Protection - Certificate Status: This matrix displays findings for hosts with expired certificates, certificates that are expiring soon, untrusted certificates and self-signed certificates. Expired certificates and other certificate problems cause a denial of service, man-in-the-middle, and trust-related concerns for organizations.
Data Protection - Removable Media noexec, nosuid, nodev Compliance: This table focuses on compliance data, filtering on regex for plugins containing: noexec, nosuid, and nodev in the plugin name. When an audit file is imported into SecurityCenter the 'description' line for the check becomes the plugin name. The description for each check provides a statement of the audit check.
Data Protection - Confidentiality of Protected Information Concerns: This table focuses on compliance data, filtering on cross references related to the Confidentiality of Protected Information. The table displays the Plugin Name, Severity, and Total, sorted by the total number of vulnerabilities identified.