by Josef Weiss
The Cyber Essentials is a UK government-backed framework which is designed to assist organisations in protecting themselves against common threats. The Cyber Essentials provides a basic cyber security foundation that can serve as a stepping stone to a more comprehensive zero-trust approach. The Cyber Essentials is built on 5 key components that, when implemented correctly, can reduce cyber risk. The five key components are:
- Firewalls and Boundary Devices
- Secure Configurations
- Access Control
- Malware Protection
- Patch Management
Tenable has released a series of dashboards, that focuses on each of the five basic technical controls, which organisations can use to help strengthen their defences against the most common cyber threats.
The focus of this dashboard is Section 5 - Patch Management. Organisations which comply with Section 5 ensure they are actively fixing vulnerabilities before attackers can exploit them, reducing risk, and demonstrating responsible security practices. In addition to reducing risk, compliance demonstrates that organisations take security seriously, improving trust with customers, partners, and regulators.
This key component applies to all the following in scope devices: Boundary Firewalls, Desktop Computers, Laptops, Routers, Servers, Iaas, PaaS, and SaaS devices. Some items to focus on within this key component are:
- Reducing exploitable weaknesses
- Keeping devices and software secure
- Limiting the window of risk (enforcing timely updates)
Widgets
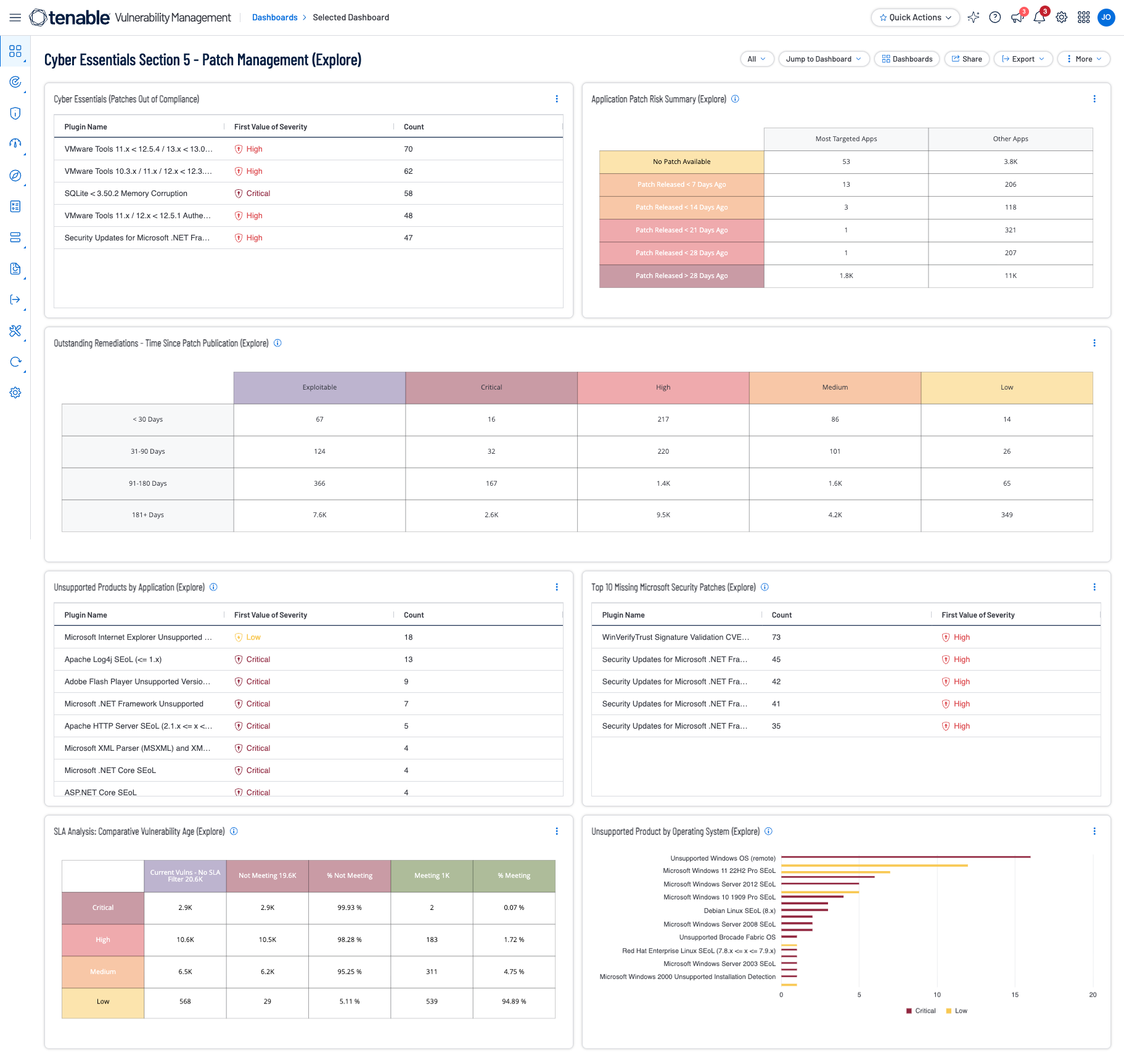
Cyber Essentials (Patches Out of Compliance) - This widget provides a detailed analysis of application vulnerabilities by comparing patch availability and release timelines for all identified application vulnerabilities where a vendor patch has been released over 14 days ago, with a CVSSv3 Score of 7.0 or greater.
Outstanding Remediations - Time Since Patch Publication - The Outstanding Remediations - Time Since Patch Publication widget displays the total count of missing patches across the environment.
Application Patch Risk Comparison - The Application Patch Risk Comparison widget provides a detailed analysis of application vulnerabilities by comparing patch availability and release timelines between 'Most Targeted Apps' and 'Other Apps.'
Unsupported Products by Application - The Unsupported Products by Application table displays top 200 unsupported applications by plugin name, sorted by count.
Unsupported Products by Operating System - The Unsupported Products by Operating System chart displays all unsupported operating systems, severity, sorted by count.
SLA Analysis: Comparative Vulnerability Age - The SLA Analysis: Comparative Vulnerability Age (Explore) helps organizations understand and analyze their risk mitigation SLA actions.
Top 50 Missing Microsoft Security Patches - This component displays the top 50 most common missing Microsoft security patches.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success