Cybersecurity Snapshot: U.S. Gov’t Unpacks AI Threat to Banks, as NCSC Urges OT Teams to Protect Cloud SCADA Systems

Check out new guidance for banks on combating AI-boosted fraud. Plus, how to cut cyber risk when migrating SCADA systems to the cloud. Meanwhile, why CISA is fed up with SQLi flaws. And best practices to prevent and respond to DDoS attacks. And much more!
Dive into six things that are top of mind for the week ending March 29.
1 - U.S. gov’t: AI is empowering financial fraudsters
Saying that artificial intelligence is supercharging financial fraud, the U.S. Treasury Department has issued a report aimed at helping banks and other financial institutions address this emerging AI threat.
The 52-page report, titled “Managing Artificial Intelligence-Specific Cybersecurity Risks in the Financial Services Sector,” touches on cybersecurity and fraud protection; fraud threats; the regulatory landscape; and major challenges and opportunities.
The report also devotes an entire section to best practices, including:
- Include AI risk management within your organization’s broader enterprise risk management program.
- Develop and implement an AI risk management framework tailored specifically for your organization and its use cases.
- Add AI-specific questions to your vendor risk-management questionnaire and processes to assess AI risks and issues, such as:
- AI technology integration
- data privacy
- data retention policies
- AI model validation
- AI model maintenance
In a statement, the Treasury Department said that it will address the AI challenges outlined in the report by collaborating with private sector companies, federal government agencies, international partners and other stakeholders.
For more information about AI-fueled financial fraud:
- “Artificial Intelligence (AI) and Investment Fraud” (FINRA)
- “How AI is Changing the Financial Crime Landscape” (FinTech Magazine)
- “AI heralds the next generation of financial scams” (Financial Times)
- “Financial fraud is exploding, fueled by cheap and easy generative AI tools” (Biometric Update)
- “AI is making financial scams harder to detect (Yahoo Finance)
2 - NCSC: How to secure cloud-hosted SCADA systems
As the trend of moving industrial applications to the cloud gathers speed, the U.K.’s cyber agency is warning operational technology (OT) teams to prioritize cybersecurity.
This week, the U.K. National Cyber Security Centre (NCSC) issued guidance on cloud-hosted supervisory control and data acquisition (SCADA) systems, stressing that cybersecurity must be “a key consideration” with these migrations.
“The current state of play in OT can make the path to securely implementing a cloud migration challenging,” the NCSC said in a blog titled “SCADA 'in the cloud': new guidance for OT organisations.”

Challenges for SCADA cloud migrations include OT teams’ reliance on legacy technology, on-prem systems and “monolithic” software, the blog reads.
NCSC’s guidance seeks to help organizations weigh three key areas when considering a SCADA cloud migration:
- Understand your business “use case”, including drivers and opportunities, so that the appropriate security controls can be implemented.
- Assess your organization’s “readiness” to support a SCADA shift to the cloud, including the necessary skills and policies.
- Determine if your existing SCADA technology is suitable for a cloud migration, and how a cloud system should be architected.
“Moving to the cloud doesn’t simply change where a SCADA system is hosted; it fundamentally alters the traditional management, security boundaries, connectivity model, and access control mechanisms, as the system is now internet-connected,” reads the guidance, titled simply “Cloud-hosted supervisory control and data acquisition.”
For more information about OT security, check out these Tenable resources:
- “Accidental Convergence - A Guide To Secured IT/OT Operations” (white paper)
- “How to Tackle OT Challenges: Asset Inventory and Vulnerability Assessment” (blog)
- “Discover, Measure, and Minimize the Risk Posed by Your Interconnected IT/OT/IoT Environments” (on-demand webinar)
- “A Practical Way To Reduce Risk on the Shop Floor” (blog)
- “How To Secure All of Your Assets - IT, OT and IoT - With an Exposure Management Platform” (blog)
VIDEOS
The Business Risk From a Ransomware Attack on OT Systems
The top threats to ICS systems
3 - CISA, FBI to tech vendors: Enough with the SQLi flaws
It’s high time for software developers to stop delivering web apps with the well-known SQL injection (SQLi) flaw, which MITRE described as an “unforgivable” software mistake way back in 2007.
That’s according to the joint alert “Secure by Design Alert - Eliminating SQL Injection Vulnerabilities in Software,” issued this week by the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI.)
“Despite widespread knowledge and documentation of SQLi vulnerabilities over the past two decades, along with the availability of effective mitigations, software manufacturers continue to develop products with this defect,” CISA and the FBI said in a statement.

The alert was prompted by the SQLi vulnerabilities that Progress Software disclosed in its MOVEit Transfer product last year. One of the bugs was exploited in the wild by the CL0P ransomware gang.
The agencies want tech vendors to review their products’ software to identify instances of SQLi flaws, and if they detect any, to quickly mitigate them. The FBI and CISA are also encouraging customers to ask their tech vendors whether they’ve assessed their software for SQLi flaws.
A SQLi flaw allows attackers to tamper with backend databases by inserting malicious SQL code into an application’s database-query inputs. Among other things, a hacker could steal, delete and corrupt the database’s information.
The solution? When crafting an application, use parameterized queries to ensure the application doesn’t treat user inputs as executable code, CISA and the FBI recommend.
For more information about SQLi attacks:
- “SQLi Injection Prevention Cheat Sheet” (OWASP)
- “How to prevent SQL injection with prepared statements” (TechTarget)
- “CWE-89: Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')” (MITRE)
- “FAQ for MOVEit Transfer Vulnerabilities and CL0P Ransomware Gang” (Tenable)
- “SQL Injection (Tenable)
VIDEO
What is SQL injection? - Web Security Academy
4 - DDoS prevention guide gets updated with new categories, mitigations
Has it been a while since you refreshed your playbook for preventing and responding to distributed denial of service (DDoS) attacks? You might find new information in the updated guide “Understanding and Responding to Distributed Denial-Of-Service Attacks” from CISA and the FBI.
The agencies, which first published the guide in March 2022, released a new version this week that categorizes DDoS attacks into three buckets, offering deeper insights and details into each. The updated document also adds recommended mitigations.
The guide now groups attacks into these categories:
- Volume-based attacks, which overwhelm the targeted system with traffic and soak up all or most of its bandwidth to impair its network performance
- Protocol-based attacks, which exploit weak network-protocol implementations to cause the targeted system to malfunction
- Application layer-based attacks, which target flaws in the targeted system’s applications or services to disrupt their operations
Recommended preventive steps to take include:
- Assessing the organization’s risk to a DDoS attack by, for example, identifying vulnerabilities in the network’s infrastructure, systems and applications
- Updating software and applying patches to fix known vulnerabilities
- Adopting secure coding practices and conducting security scans of web applications
- Implementing network monitoring tools and intrusion detection systems
- Conducting regular analysis of network traffic patterns
- Adding a captcha challenge to your websites and online services
If your organization is hit by a DDoS attack, CISA’s response advice includes:
- Identify what type of DDoS attack it is and activate your incident response plan
- Notify your internet and hosting providers
- Implement traffic filtering measures and, if possible, scale up bandwidth
- Use a content delivery network (CDN) to absorb and distribute traffic
For more information about DDoS attacks:
- “Preparing for denial of service (DoS) attacks” (U.K. NCSC)
- “How to Prevent DDoS Attacks: 5 Steps for DDoS Prevention” (eSecurity Planet)
- “Protecting your organization against denial of service attacks” (Canadian Centre for Cyber Security)
- “What is a DDoS attack?” (TechTarget)
5 - A quick look at CTEM in identity security
During our recent webinar “Why You Need Contextual Intelligence in the Age of Identity-First and Zero Trust Security,” we took the opportunity to ask respondents about continuous threat exposure management (CTEM) in the context of identity security. Check out what they said about their risk prioritization programs and about their CTEM maturity.
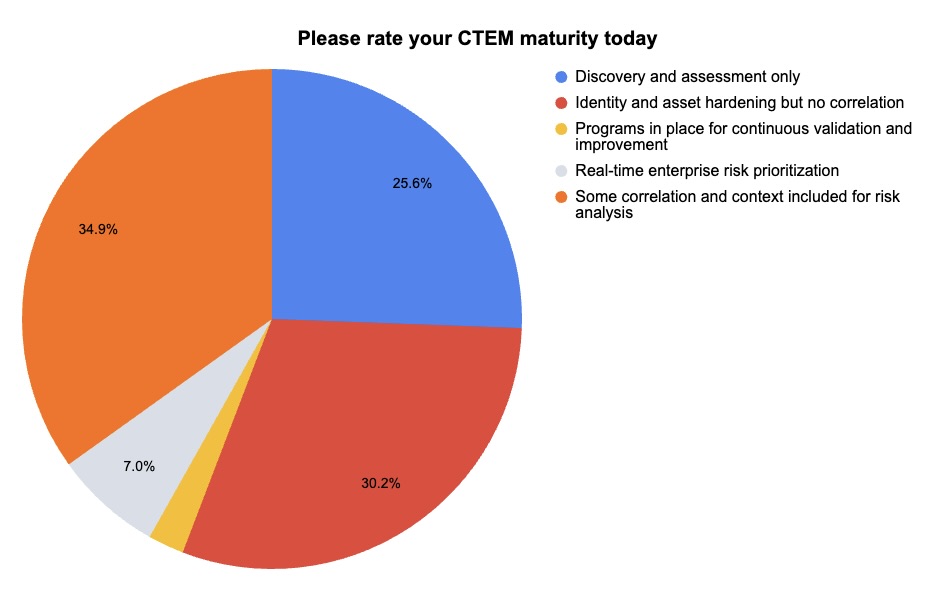
(43 respondents polled by Tenable, March 2024)
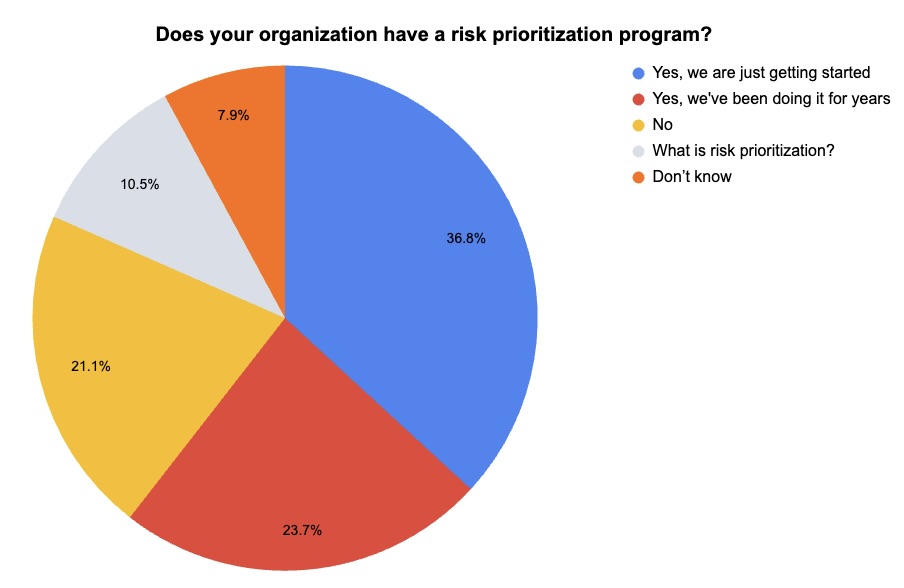
(38 respondents polled by Tenable, March 2024)
Interested in learning how to operationalize identity security to achieve accurate real-time risk prioritization and CTEM? Watch the webinar on-demand!
6 - Google: Zero-day bugs exploited in the wild rose 50%-plus in 2023
For those of you tracking the prevalence of zero-day bugs that attackers exploit, here are some 2023 stats Google released this week that you might find interesting.
- Last year, Google observed 97 zero-day vulnerabilities that were exploited in the wild, up 56% from 2022, but a bit short of the 106 observed in 2021.
- Attackers placed a heavier emphasis on exploiting zero-day bugs present in:
- third-party components and libraries, because they offer the chance to breach multiple products and targets
- enterprise software products
- In terms of nation-state attackers, those backed by the Chinese government ranked first with 12 zero-day bugs exploited in the wild.
“Exploiting zero-days is no longer a niche capability. The proliferation of exploit technology makes this troubling threat available to more actors around the world,” reads a Google blog about the zero-day bug report.
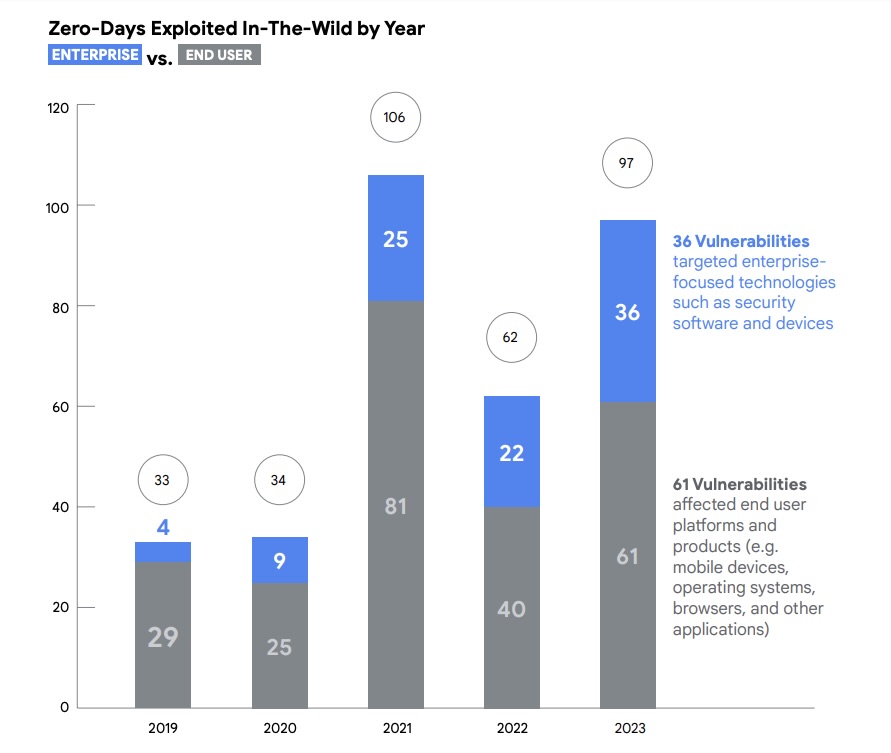
(Source: “A Year in Review of Zero-Days Exploited In-the-Wild in 2023” report from Google, March 2024)
In terms of recommendations, the report encourages software vendors to be fully transparent, promptly disclosing vulnerabilities and issuing patches; and to have a prepared plan for responding if a zero-day bug is found in one of their products.
Meanwhile, cybersecurity teams are advised to prioritize the threats with the biggest potential to cause damage; and to ensure they’ve built a strong security foundation.
- Cloud
- Cybersecurity Snapshot
- Federal
- Government
- Internet of Things
- OT Security
- SCADA
- Vulnerability Management

